Deets On The Precision Algorithm for Threat Recognition and Information Oversight Technology Strategic Homeland Information and Enforcement Logistics Division (P.A.T.R.I.O.T. S.H.I.E.L.D.) Cyber Act
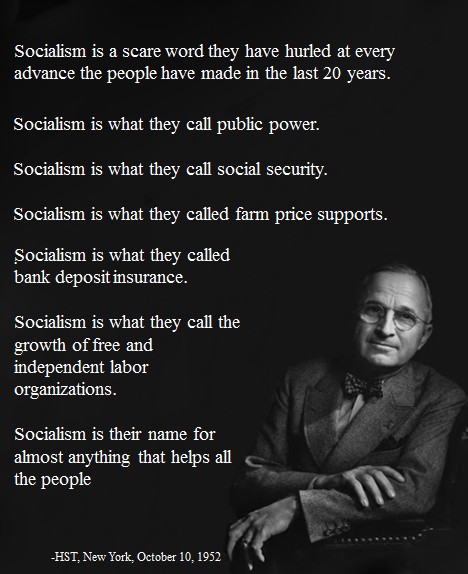
Deets On The Fair Deal
Deets On The Precision Algorithm for Threat Recognition and Information Oversight Technology Strategic Homeland Information and Enforcement Logistics Division (P.A.T.R.I.O.T. S.H.I.E.L.D.) Cyber Act

Deets On The Precision Algorithm for Threat Recognition and Information Oversight Technology Strategic Homeland Information and Enforcement Logistics Division (P.A.T.R.I.O.T. S.H.I.E.L.D.) Cyber Act
Whereas the United States of America recognizes the critical importance of safeguarding its cyber infrastructure, digital discourse, and democratic institutions from malicious actors seeking to undermine national security, sow discord, and erode public trust;
Whereas the proliferation of disinformation, misinformation, and hate speech across digital platforms poses significant threats to the integrity of democratic processes, social cohesion, and individual liberties;
Whereas cyber threats, including but not limited to hacking, cyber espionage, and cyber warfare, present ongoing challenges to the security and stability of the nation's cyber infrastructure, including critical systems such as the national power grid;
Whereas it is imperative for the United States to develop and deploy advanced technologies and strategies to detect, mitigate, and counter these threats in real-time, while simultaneously upholding the fundamental principles of free speech, privacy, and the rule of law;
Whereas the establishment of a comprehensive cyber firewall system, under the auspices of the Precision Algorithm for Threat Recognition and Information Oversight Technology Strategic Homeland Information and Enforcement Logistics Division (P.A.T.R.I.O.T. S.H.I.E.L.D.), is deemed necessary to address these pressing challenges and protect the interests of the American people;
Now, therefore, be it enacted by the Congress and the President of the United States that the following bill is proposed to establish P.A.T.R.I.O.T. S.H.I.E.L.D. within the Department of Homeland Security, with the mandate to detect, remove, and counter disinformation, misinformation, hate speech, and cyber threats to national security in real-time.
Section 1: Establishment of P.A.T.R.I.O.T. S.H.I.E.L.D.
1.1. There shall be established within the Department of Homeland Security (DHS) the Precision Algorithm for Threat Recognition and Information Oversight Technology Strategic Homeland Information and Enforcement Logistics Division (P.A.T.R.I.O.T. S.H.I.E.L.D.), herein referred to as "P.A.T.R.I.O.T. S.H.I.E.L.D.".
1.2. P.A.T.R.I.O.T. S.H.I.E.L.D. shall be a specialized division dedicated to the development, implementation, and maintenance of cutting-edge technologies and methodologies aimed at protecting the United States' cyber infrastructure, digital discourse, and democratic institutions from threats such as disinformation, misinformation, hate speech, and cyber attacks.
1.3. The primary objective of P.A.T.R.I.O.T. S.H.I.E.L.D. shall be to deploy advanced algorithms and countermeasures capable of detecting, analyzing, and mitigating malicious activities in real-time, thereby safeguarding the integrity of digital communication channels, preserving public trust, and upholding national security interests.
1.4. P.A.T.R.I.O.T. S.H.I.E.L.D. shall collaborate closely with other relevant government agencies, academic institutions, private sector entities, and international partners to leverage expertise, resources, and intelligence in the pursuit of its mission.
1.5. The establishment of P.A.T.R.I.O.T. S.H.I.E.L.D. shall be funded through appropriations allocated to the Department of Homeland Security for the purpose of enhancing national cybersecurity capabilities and addressing emerging threats in the digital domain.
1.6. P.A.T.R.I.O.T. S.H.I.E.L.D. shall operate under the authority and oversight of the Department of Homeland Security, in accordance with applicable laws, regulations, and constitutional principles, including protections for civil liberties, privacy rights, and freedom of expression.
Section 2: Functions and Responsibilities
2.1. Detection and Removal:
2.1.1. P.A.T.R.I.O.T. S.H.I.E.L.D. shall develop and deploy sophisticated algorithms and analytical tools capable of identifying, categorizing, and removing disinformation, misinformation, and hate speech disseminated through digital channels, including social media platforms, websites, and online forums.
2.1.2. These algorithms shall be continuously updated and refined to adapt to evolving tactics employed by malicious actors, leveraging artificial intelligence, machine learning, natural language processing, and data analytics techniques to enhance accuracy and effectiveness.
2.1.3. P.A.T.R.I.O.T. S.H.I.E.L.D. shall collaborate with digital platform providers, internet service providers, and telecommunications companies to facilitate the integration of its detection and removal technologies into existing infrastructure, ensuring seamless and comprehensive coverage across digital ecosystems.
2.2. Countermeasures:
2.2.1. P.A.T.R.I.O.T. S.H.I.E.L.D. shall develop and implement real-time countermeasures to mitigate cyber threats targeting the national cyber infrastructure and critical systems, including the power grid, financial networks, and government databases.
2.2.2. These countermeasures shall encompass a range of defensive strategies, including but not limited to:
a) Intrusion detection systems (IDS) and intrusion prevention systems (IPS) to identify and block unauthorized access attempts and suspicious activities.
b) Threat intelligence sharing initiatives to facilitate information exchange and collaboration among government agencies, private sector entities, and international partners.
c) Incident response protocols and emergency preparedness measures to ensure rapid, coordinated responses to cyber attacks and breaches, minimizing the impact on national security and public safety.
2.2.3. P.A.T.R.I.O.T. S.H.I.E.L.D. shall conduct regular assessments of cyber vulnerabilities and emerging threats, employing proactive measures such as penetration testing, vulnerability scanning, and threat hunting to identify and address potential weaknesses in the nation's cyber defenses.
2.2.4. P.A.T.R.I.O.T. S.H.I.E.L.D. shall engage in research and development activities to explore innovative technologies and strategies for enhancing cyber resilience, including blockchain technology, quantum encryption, and secure software development practices.
2.2.5. P.A.T.R.I.O.T. S.H.I.E.L.D. shall collaborate with critical infrastructure operators, regulatory agencies, and cybersecurity experts to promote the adoption of best practices and standards for cyber hygiene, risk management, and incident response across all sectors of the economy.
2.2.6. P.A.T.R.I.O.T. S.H.I.E.L.D. shall maintain a comprehensive cyber threat intelligence database, collecting, analyzing, and disseminating actionable intelligence to support decision-making processes and enhance situational awareness at all levels of government and industry.
2.2.7. P.A.T.R.I.O.T. S.H.I.E.L.D. shall engage in public outreach and education efforts to raise awareness about cyber threats, promote responsible digital citizenship, and empower individuals and organizations to take proactive steps to protect themselves against cyber attacks and online exploitation.
See:
Section 3: Repeal of Section 230 and Establishment of Public Content Moderation Service
3.1. Repeal of Section 230:
3.1.1. Upon full operationalization of P.A.T.R.I.O.T. S.H.I.E.L.D. and the establishment of the Public Content Moderation Service (PCMS) as outlined in this Act, Section 230 of the Communications Decency Act shall be repealed.
3.1.2. The repeal of Section 230 shall remove legal immunities currently granted to social media platforms and other online intermediaries, holding them accountable for content hosted on their platforms while providing safeguards to protect freedom of expression and due process rights.
3.1.3. Congress shall enact complementary legislation to establish liability standards and procedural safeguards for content moderation activities conducted by social media platforms and other online service providers, ensuring fairness, transparency, and accountability in the enforcement of community standards and content policies.
3.2. Establishment of Public Content Moderation Service:
3.2.1. In conjunction with the repeal of Section 230, the Federal Government shall establish the Public Content Moderation Service (PCMS) as a dedicated, impartial, and professionally staffed entity responsible for overseeing content moderation activities on social media platforms and other digital communication channels.
3.2.2. The PCMS shall operate under the jurisdiction of the Department of Homeland Security and shall be administered as part of the broader framework of P.A.T.R.I.O.T. S.H.I.E.L.D., leveraging its expertise, resources, and infrastructure to enhance the effectiveness and efficiency of content moderation efforts.
3.2.3. Content moderators employed by the PCMS shall be recruited from diverse backgrounds and shall undergo rigorous vetting processes, including background checks, security clearances, and specialized training in areas such as cyber hygiene, cultural competence, and conflict resolution.
3.2.4. The PCMS shall develop and implement standardized procedures and best practices for content moderation, including guidelines for assessing the legality, appropriateness, and context of user-generated content, while respecting the principles of freedom of expression, privacy, and diversity of viewpoints.
3.2.5. The PCMS shall collaborate with social media companies, civil society organizations, academic institutions, and international partners to share insights, exchange best practices, and develop innovative solutions to address emerging challenges and trends in online content moderation.
3.2.6. Funding for the establishment and operation of the PCMS shall be allocated from appropriations made available to the Department of Homeland Security for the operation and maintenance of P.A.T.R.I.O.T. S.H.I.E.L.D., with dedicated resources provided to support recruitment, training, technology acquisition, and ongoing operational expenses.
3.2.7. The PCMS shall operate with transparency, accountability, and impartiality, adhering to legal standards, ethical principles, and human rights norms in its content moderation activities, while promoting public trust, safety, and resilience in the digital environment.
3.3. Detection, Handling, and Reporting of Child Sexual Abuse Material (CSAM):
3.3.1. The Public Content Moderation Service (PCMS) shall prioritize the detection, handling, and reporting of Child Sexual Abuse Material (CSAM) in accordance with federal laws, including the PROTECT Our Children Act and the Child Abuse Prevention and Treatment Act (CAPTA), and international conventions, such as the Convention on the Rights of the Child.
3.3.2. PCMS shall employ advanced technologies, including image hashing, machine learning algorithms, and content recognition software, to proactively identify and remove CSAM from online platforms and digital communication channels, while minimizing the risk of false positives and unintended censorship.
3.3.3. PCMS shall collaborate with law enforcement agencies, including the National Center for Missing and Exploited Children (NCMEC) and the Internet Crimes Against Children (ICAC) Task Forces, to facilitate the rapid reporting and investigation of CSAM incidents, ensuring timely intervention and assistance for victims.
3.3.4. PCMS shall establish clear protocols and procedures for handling and reporting CSAM incidents, including the preservation of evidence, chain of custody, and compliance with legal requirements for reporting to appropriate authorities, while prioritizing the safety and well-being of child victims and survivors.
3.3.5. PCMS shall provide training and support to content moderators and other personnel involved in CSAM detection and reporting, including trauma-informed care, psychological support, and resources for self-care, to mitigate the potential impact of exposure to graphic and disturbing content.
3.3.6. PCMS shall maintain transparency and accountability in its CSAM detection and reporting activities, regularly publishing data on the volume, nature, and outcomes of CSAM incidents identified and addressed by the service, while respecting the privacy and dignity of victims and survivors.
Section 4: Real-Time Terrorism Communications Detection and Monitoring
4.1. Purpose:
4.1.1. Recognizing the paramount importance of safeguarding national security and preventing acts of terrorism, this section establishes provisions for the real-time detection and monitoring of domestic and international terrorism communications while upholding Constitutional principles and protections.
4.2. Constitutional Guidelines:
4.2.1. All activities conducted pursuant to this section shall fully adhere to the principles and protections outlined in the Constitution of the United States, including but not limited to the First Amendment's protections for freedom of speech, freedom of the press, and freedom of association.
4.2.2. The detection and monitoring of terrorism communications shall be conducted in a manner consistent with the Fourth Amendment's protections against unreasonable searches and seizures, requiring adherence to lawful warrants, probable cause standards, and judicial oversight.
4.2.3. The rights to due process, privacy, and equal protection under the law shall be respected and upheld throughout all stages of the detection and monitoring process, ensuring that individuals subject to surveillance are afforded appropriate legal protections and remedies.
4.3. Establishment of Terrorism Communications Detection and Monitoring Program:
4.3.1. The Department of Homeland Security, in collaboration with relevant intelligence and law enforcement agencies, shall establish a program for the real-time detection and monitoring of domestic and international terrorism communications, herein referred to as the Terrorism Communications Detection and Monitoring Program (TCDMP).
4.3.2. TCDMP shall deploy advanced technologies and methodologies to identify, analyze, and track communications associated with known or suspected terrorist individuals, groups, organizations, or networks, with a focus on detecting and disrupting potential threats to national security.
4.3.3. TCDMP shall operate under the authority and oversight of the Department of Homeland Security, with appropriate checks and balances to ensure compliance with Constitutional guidelines, statutory requirements, and ethical standards, including protections for civil liberties and privacy rights.
4.4. Legal and Oversight Framework:
4.4.1. TCDMP shall be subject to robust legal and oversight mechanisms to ensure transparency, accountability, and adherence to Constitutional principles, including regular review by independent oversight bodies, judicial scrutiny of surveillance activities, and reporting requirements to Congress.
4.4.2. Any information collected or derived from terrorism communications detection and monitoring activities shall be handled and disseminated in accordance with applicable laws, regulations, and policies, with appropriate safeguards to protect sensitive information and prevent unauthorized disclosure.
4.4.3. Individuals or entities subject to surveillance under TCDMP shall have the right to challenge the legality of such surveillance and seek judicial remedies for any violations of their Constitutional rights, including the right to petition for redress of grievances and seek injunctive relief or damages.
4.5. International Cooperation and Coordination:
4.5.1. TCDMP shall collaborate with international partners, including foreign governments, intelligence agencies, and law enforcement entities, to enhance the detection and monitoring of transnational terrorism communications, facilitate information sharing, and support joint investigative efforts.
4.5.2. International cooperation shall be conducted in accordance with established legal frameworks, bilateral agreements, and diplomatic protocols, respecting the sovereignty, laws, and human rights of partner countries while advancing common security interests and objectives.
Section 5: Oversight and Accountability
5.1. P.A.T.R.I.O.T. S.H.I.E.L.D. shall operate under robust oversight mechanisms to ensure transparency, accountability, and adherence to legal and constitutional standards.
5.2. Oversight Bodies:
5.2.1. An independent review board shall be established to provide impartial oversight of P.A.T.R.I.O.T. S.H.I.E.L.D.'s activities, including its use of algorithms, data collection practices, and enforcement actions.
5.2.2. The review board shall consist of cybersecurity experts, legal scholars, civil liberties advocates, and representatives from relevant government agencies, appointed by Congress and the President, with staggered terms to ensure continuity and independence.
5.2.3. The review board shall have the authority to conduct periodic audits, investigations, and hearings to evaluate P.A.T.R.I.O.T. S.H.I.E.L.D.'s compliance with statutory requirements, constitutional principles, and ethical standards.
5.2.4. The review board shall issue regular reports to Congress and the public on its findings, recommendations, and concerns regarding P.A.T.R.I.O.T. S.H.I.E.L.D.'s performance, effectiveness, and impact on civil liberties and democratic norms.
5.3. Congressional Oversight:
5.3.1. The relevant congressional committees, including but not limited to the House Committee on Homeland Security and the Senate Committee on Homeland Security and Governmental Affairs, shall exercise oversight authority over P.A.T.R.I.O.T. S.H.I.E.L.D.'s activities, budget, and policies.
5.3.2. Congressional hearings shall be held periodically to review P.A.T.R.I.O.T. S.H.I.E.L.D.'s operations, receive testimony from agency officials and external stakeholders, and assess the need for legislative reforms or adjustments to the agency's mandate.
5.3.3. Congress shall have the power to subpoena documents, compel witness testimony, and enact legislation to address concerns raised by oversight bodies and the public regarding P.A.T.R.I.O.T. S.H.I.E.L.D.'s conduct, decisions, or impact on civil liberties.
5.4. Judicial Review:
5.4.1. P.A.T.R.I.O.T. S.H.I.E.L.D.'s actions, including the use of algorithms to detect and remove content, shall be subject to judicial review to ensure compliance with constitutional rights, including the First Amendment's protections for free speech and freedom of the press.
5.4.2. Individuals or entities aggrieved by P.A.T.R.I.O.T. S.H.I.E.L.D.'s enforcement actions may seek judicial remedies, including injunctive relief, declaratory judgments, and damages, in federal courts.
5.4.3. Courts shall apply rigorous scrutiny to P.A.T.R.I.O.T. S.H.I.E.L.D.'s decisions and procedures, considering factors such as the accuracy of algorithms, the adequacy of due process protections, and the necessity of restrictions on speech or expression to achieve legitimate government interests.
5.5. Open Source Code Requirement:
5.5.1. P.A.T.R.I.O.T. S.H.I.E.L.D. shall ensure transparency and accountability in its technology development and implementation by making its code open source in areas that do not endanger national security or jeopardize the privacy and safety of innocent citizens.
5.5.2. The Department of Homeland Security, in consultation with relevant stakeholders, shall identify portions of P.A.T.R.I.O.T. S.H.I.E.L.D.'s codebase that can be made publicly accessible without compromising operational security or disclosing sensitive information.
5.5.3. Open source code shall be subject to rigorous review by independent experts, cybersecurity researchers, and civil society organizations to identify vulnerabilities, assess algorithmic biases, and ensure compliance with legal and ethical standards.
5.5.4. P.A.T.R.I.O.T. S.H.I.E.L.D. shall establish mechanisms for soliciting feedback, contributions, and improvements from the broader technology community, fostering collaboration and innovation in the development and refinement of its algorithms, tools, and systems.
5.5.5. The Department of Homeland Security shall periodically evaluate the impact and effectiveness of open source code initiatives within P.A.T.R.I.O.T. S.H.I.E.L.D., including their contribution to transparency, accountability, and public trust, and shall make adjustments as necessary to optimize their benefits while mitigating any potential risks.
Section 6: Funding
6.1. Appropriations:
6.1.1. The Department of Homeland Security shall receive appropriations from Congress for the establishment, operation, and maintenance of P.A.T.R.I.O.T. S.H.I.E.L.D., including but not limited to funding for personnel, technology acquisition, research and development, and ongoing operational expenses.
6.1.2. Appropriations shall be made available on an annual basis, with sufficient flexibility to accommodate unforeseen contingencies, emerging threats, and evolving technology requirements.
6.2. Funding Allocation:
6.2.1. A portion of the appropriations shall be allocated for research and development activities aimed at advancing the capabilities of P.A.T.R.I.O.T. S.H.I.E.L.D. in detecting and mitigating cyber threats, improving the accuracy and efficiency of algorithms, and enhancing collaboration with external stakeholders.
6.2.2. Another portion of the appropriations shall be allocated for personnel training and capacity-building initiatives, including recruitment, retention, and professional development programs for cybersecurity specialists, data analysts, legal experts, and other staff members.
6.2.3. Additionally, funding shall be allocated for technology acquisition and infrastructure upgrades to support the deployment and operation of P.A.T.R.I.O.T. S.H.I.E.L.D.'s detection and removal systems, including hardware, software, cloud computing services, and data storage solutions.
6.2.4. Ongoing operational expenses, such as maintenance, utilities, and administrative costs, shall also be covered by the appropriations, ensuring the uninterrupted functioning of P.A.T.R.I.O.T. S.H.I.E.L.D. and its ability to fulfill its mission effectively.
6.3. Accountability Measures:
6.3.1. The Department of Homeland Security shall be responsible for ensuring transparent and accountable use of appropriated funds, including proper documentation, reporting, and auditing of expenditures related to P.A.T.R.I.O.T. S.H.I.E.L.D.
6.3.2. Financial statements and performance reports shall be submitted to Congress and the Government Accountability Office (GAO) on a regular basis, detailing the use of funds, progress towards stated objectives, and outcomes achieved by P.A.T.R.I.O.T. S.H.I.E.L.D.
6.3.3. Congress shall exercise oversight authority to monitor the allocation and expenditure of funds, evaluate the effectiveness of resource utilization, and identify opportunities for budgetary adjustments or reallocations to optimize the performance of P.A.T.R.I.O.T. S.H.I.E.L.D.
Section 7: Implementation
7.1. Timeline:
7.1.1. The Department of Homeland Security shall commence the establishment of P.A.T.R.I.O.T. S.H.I.E.L.D. immediately upon enactment of this Act.
7.1.2. Within three months of enactment, the Department shall convene an interagency task force comprised of cybersecurity experts, legal advisors, technology specialists, and other relevant stakeholders to develop a comprehensive implementation plan for P.A.T.R.I.O.T. S.H.I.E.L.D.
7.1.3. The implementation plan shall outline key milestones, deliverables, and resource requirements for the establishment, operationalization, and initial deployment of P.A.T.R.I.O.T. S.H.I.E.L.D., ensuring alignment with the objectives and provisions of this Act.
7.1.4. Within six months of enactment, the Department shall complete the establishment and operationalization of P.A.T.R.I.O.T. S.H.I.E.L.D., including the deployment of detection and removal systems, establishment of oversight mechanisms, and commencement of collaborative efforts with external partners.
7.2. Procedural Guidelines:
7.2.1. The Department shall establish clear procedural guidelines and protocols governing the operations of P.A.T.R.I.O.T. S.H.I.E.L.D., including procedures for content moderation, data handling, enforcement actions, and appeals processes.
7.2.2. These guidelines shall be developed in consultation with legal experts, civil liberties advocates, and other stakeholders to ensure compliance with constitutional rights, statutory requirements, and ethical standards, including protections for free speech, privacy, and due process.
7.2.3. The guidelines shall be made publicly available and regularly reviewed and updated to reflect evolving legal and policy considerations, technological advancements, and feedback from oversight bodies and the public.
7.3. Coordination and Collaboration:
7.3.1. The Department shall establish mechanisms for coordinating and collaborating with federal, state, local, tribal, and territorial governments, as well as international partners, industry stakeholders, and civil society organizations, to maximize the effectiveness and impact of P.A.T.R.I.O.T. S.H.I.E.L.D.
7.3.2. Interagency working groups shall be established to facilitate information sharing, joint operations, and coordinated responses to cyber threats, ensuring a unified and cohesive approach across all levels of government and sectors of society.
7.4. Training and Capacity Building:
7.4.1. The Department shall prioritize training and capacity-building initiatives to enhance the skills, knowledge, and capabilities of P.A.T.R.I.O.T. S.H.I.E.L.D. personnel, including cybersecurity specialists, data analysts, legal advisors, and outreach coordinators.
7.4.2. Training programs shall cover a range of topics, including cyber threat detection, algorithmic analysis, legal compliance, cultural sensitivity, and crisis management, tailored to the specific roles and responsibilities of each staff member within P.A.T.R.I.O.T. S.H.I.E.L.D.
Section 8: Severability and Legal Protections
8.1. Severability:
8.1.1. If any provision of this Act, or the application thereof to any person or circumstance, is held invalid or unconstitutional, the remainder of the Act and the application of such provision to other persons or circumstances shall not be affected thereby.
8.1.2. The invalidity or unenforceability of any provision of this Act shall not impair or affect the validity or enforceability of the remaining provisions of the Act, which shall continue in full force and effect.
8.2. Legal Protections:
8.2.1. Nothing in this Act shall be construed to abridge the rights and protections guaranteed by the Constitution of the United States, including the First Amendment's protections for freedom of speech, freedom of the press, and freedom of association.
8.2.2. P.A.T.R.I.O.T. S.H.I.E.L.D. shall operate in accordance with established legal principles, including due process, equal protection, and the presumption of innocence, ensuring that individuals subject to enforcement actions have the opportunity to challenge the validity of such actions and seek redress for any harm suffered.
8.2.3. The use of algorithms and automated systems by P.A.T.R.I.O.T. S.H.I.E.L.D. shall be subject to rigorous scrutiny to ensure transparency, accountability, and fairness, with mechanisms in place to address algorithmic bias, errors, and unintended consequences.
8.2.4. Any restrictions on speech or expression imposed by P.A.T.R.I.O.T. S.H.I.E.L.D. shall be narrowly tailored to serve compelling government interests, such as protecting national security, public safety, and democratic institutions, and shall be subject to judicial review to assess their constitutionality and proportionality.
8.3. Reporting Requirements:
8.3.1. The Department of Homeland Security shall submit annual reports to Congress on the implementation and impact of P.A.T.R.I.O.T. S.H.I.E.L.D., including data on enforcement actions taken, content removed, appeals filed, and outcomes achieved.
8.3.2. These reports shall include an assessment of the effectiveness of P.A.T.R.I.O.T. S.H.I.E.L.D. in achieving its stated objectives, as well as any challenges or concerns identified during the reporting period, along with recommendations for legislative or policy reforms to address them.
Section 9: Enactment and Citation
9.1. Enactment:
9.1.1. This Act shall take effect immediately upon its passage by both houses of Congress and its signing into law by the President of the United States.
9.1.2. The Department of Homeland Security shall initiate the necessary actions to implement the provisions of this Act promptly upon its enactment, in accordance with the timelines and requirements specified herein.
9.2. Citation:
9.2.1. This Act may be cited as the "United States Cyber Firewall Act" or by its popular title, the "P.A.T.R.I.O.T. S.H.I.E.L.D. Cyber Act."
9.2.2. References to this Act in legal, regulatory, and administrative documents, as well as in public discourse and media reporting, may use either the full title or the popular title, as appropriate.
9.2.3. The popular title "P.A.T.R.I.O.T. S.H.I.E.L.D. Cyber Act" shall be considered the official name of the legislation for purposes of public awareness and recognition, reflecting its overarching goal of protecting national security and democratic values in the digital age.
Conclusion:
In conclusion, the United States Cyber Firewall and Social Media Content Moderation Act, also known as the P.A.T.R.I.O.T. S.H.I.E.L.D. Act, represents a pivotal step forward in safeguarding the nation's cyber infrastructure, digital discourse, and democratic institutions from malicious actors and emerging threats. By establishing the Precision Algorithm for Threat Recognition and Information Oversight Technology Strategic Homeland Information and Enforcement Logistics Division (P.A.T.R.I.O.T. S.H.I.E.L.D.) within the Department of Homeland Security, this Act aims to deploy advanced technologies and strategies to detect, remove, and counter disinformation, misinformation, hate speech, and cyber threats in real-time.
Through robust oversight mechanisms, rigorous legal protections, and proactive engagement with stakeholders, P.A.T.R.I.O.T. S.H.I.E.L.D. will uphold the fundamental principles of free speech, privacy, and the rule of law, while effectively combating threats to national security and public trust. By fostering collaboration across government agencies, industry sectors, and civil society organizations, this Act seeks to harness the collective expertise and resources necessary to confront the complex and evolving challenges posed by cyber warfare, social manipulation, and information warfare.
As the United States continues to navigate the digital landscape of the 21st century, the enactment of the United States Cyber Firewall and Social Media Content Moderation Act underscores our commitment to defending democratic values, protecting individual liberties, and ensuring the resilience and security of our digital ecosystem. By embracing innovation, accountability, and unity of purpose, we can confront the threats of tomorrow while preserving the freedoms and opportunities that define our nation today.
See:
See:
See:
See:
I am neither a lawyer nor a financial advisor and this document does not constitute legal or financial advice.
This proposal is a thought exercise and is no guarantee of either product or service.